Installation of Mend for Bitbucket Cloud
Overview
This page describes the installation process of Mend for Bitbucket Cloud.
This integration covers the Legacy SCA application for Bitbucket Cloud. Organizations on the Mend AppSec Platform should use the designated Developer Platform integration for Bitbucket Cloud.
Mend for Bitbucket Cloud is supported for customers on a Mend Dedicated Instance. Please contact your Mend sales representative.
Prerequisites
Note: Setting up global configuration is highly recommended for centralized mass deployments.
The following requirements must be accommodated before installing Mend for Bitbucket Cloud:
Access to a working Mend Application and a user with Admin privileges (either Organization or Product Admin).
“Developer Integrations” enabled in your Mend organization.
Access to Bitbucket Cloud and a user with Admin privileges in a Workspace that will be integrated.
Multiple Bitbucket workspaces can be integrated with a single Mend organization
For each repository where issues are enabled (issueSettings) the Issue Tracker must be enabled.
Python support: The default Python version supported is 3.7.12. If you have a Python project with a version that is not compatible with the default one, you can choose one of the following:
2.7.18, 3.6.15, 3.9.9,or3.11.
For this you will need to perform the following procedure:Add a .whitesource configuration file to your repository. Alternatively, you can apply this globally across your repositories by using the Global Repo Configuration.
Use the configMode parameter and set it to either LOCAL or EXTERNAL.
In the whitesource.config file, add the following:
CODEpython.invokePipAsModule=true python.path=python3.9 python.installVirtualenv=trueNOTE: For
python.pathuse one of the following values:2.7,3.6,3.7,3.9, or3.11.
Note: When setting up repository integrations, you can only connect one source code management (SCM) system to a single Mend organization. For example, if you integrate a GitHub organization, you cannot link additional SCM systems like GitLab groups or Bitbucket teams to the same Mend organization.
Pre-Installation Configuration
It is possible to skip instructions from this section and install the Mend application without them. However, it is strongly recommended to take into account this preparation before actually installing the application.
When Mend detects that there is a whitesource-config repository in the integrated Workspace, it will populate it with files global-config.json and repo-config.json that will configure the application behavior for all integrated repositories (more information about this can be found in the document Global Repo Configuration):
The global-config.json file defines the rules for how Mend should handle the global configuration for all integrated repositories. This includes what repositories should be onboarded and how, as well as any other global configuration settings.
The repo-config.json file defines the set of configurations that will be applied to each repository that uses this global configuration. This includes what vulnerabilities Mend should look for and what should happen when they are detected (e.g., whether to create security checks or issues, or whether to enable remediation pull requests).
By creating these files before installing Mend, you can customize how Mend scans your repositories during onboarding and change its default behavior. For example, you might want to specify which repositories should be onboarded so that they are all scanned immediately after installing Mend, or you might want to change how Mend handles the vulnerabilities it finds.
NOTE: You can always change these configurations later, but doing so before onboarding will affect the way the onboarding scan happens in all your repositories. If you make changes to these files after installing Mend, the changes will only take effect after a valid push is performed in each of the repositories.
Specifying repositories that should be onboarded
Create a repository named whitesource-config in any of the Projects of the Workspace where Mend will be installed.
In this repository, create the file global-config.json.
The default configuration of this file for Mend for Bitbucket cloud is:
CODE{ "repoConfigMode": "createOnboardingPR", "includedRepos": { "exactNames": [] } }Parameter
includedReposspecifies the list of repositories that should be onboarded to Mend. When it equals to"exactNames": []no repositories will be onboarded. To onboard some of the repositories list them as array items in the following way:"exactNames": ["Workspace-name/repo-name-0", "Workspace-name/repo-name-1"].
To onboard all repositories in the Workspace do not use the parameterincludedReposin the global-config.json.Alternatively, it is possible to use the parameter
ignoredReposinstead ofincludedReposwhen you want to specify repositories that should not be onboarded. If this parameter is used, all repositories that are not listed will be onboarded.CODE{ "repoConfigMode": "createOnboardingPR", "ignoredRepos": { "exactNames": ["Workspace-ID/repo-name-0", "Workspace-ID/repo-name-1"] } }
Workspace-id’s must be be taken from BitBucket. Navigate to
https://bitbucket.org/account/workspaces/, select the desired workspace and click Settings. The workspace-id can also be obtained by navigating directly tohttps://bitbucket.org/{workspace-ID}/{repository-name}.More information about this file and its parameters can be found in the document about Global Repo Configuration.
A valid commit must occur in the included repository for an onboarding pull request to be created.
When adding a new repository that was not previously included in the exactNames list, the creation of the repository's onboarding pull request will occur only after a valid push event happens in the repository.
Changing the default global configuration
The default configuration of this file for Mend for Bitbucket cloud is:
{
"scanSettings": {
"configMode": "AUTO",
"configExternalURL": "",
"baseBranches": []
},
"buildSettings": {
"createBuildStatus": true
},
"issueSettings": {
"minSeverityLevel": "LOW",
"issueType": "DEPENDENCY"
},
"remediateSettings": {
"workflowRules": {
"enabled": false
}
}
}“The .whitesource File” section of this document covers information on what these parameters mean and what can be added to the repo-config.json file.
Installing Mend for Bitbucket Cloud
Install the application to a Bitbucket Cloud Workspace by clicking on this link.
You will be redirected to a “Mend for Bitbucket Cloud Registration“ page where you need to insert a License Key.
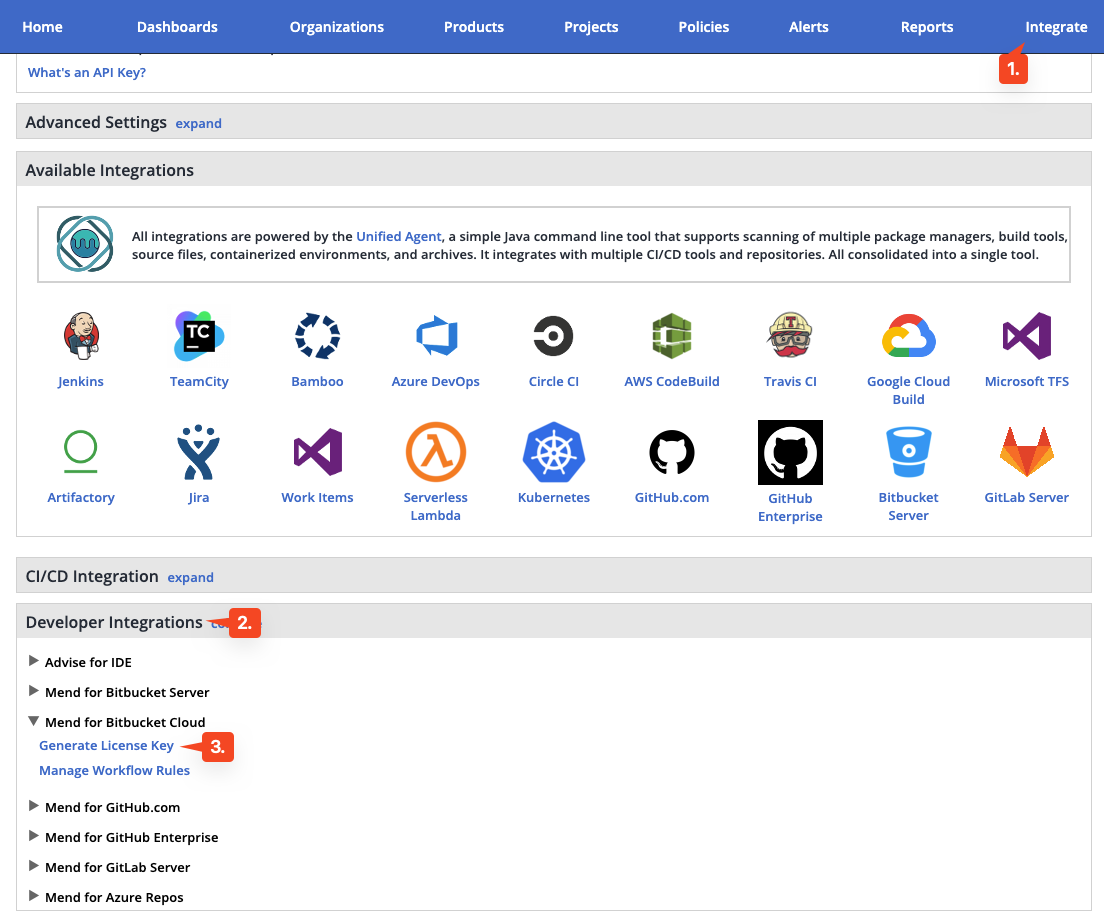
To obtain your license key, open the Mend 'Integrate' page or get the license key from your Administrator (if you are not a Mend Admin).
Click on 'Generate License Key' from the 'Mend for Bitbucket Cloud' section and paste the copied license key into the field on the Registration page.
After the License Key is provided on the Registration page, the application will be installed in the Workspace.
If instructions from “Pre-installation configuration” were skipped, create a repository named whitesource-config in any of the Projects of the Workspace where Mend was installed. It will be populated with configuration files global-config.json and repo-config.json. Refer to Global Repo Configuration to apply the required configuration to Mend in the integrated Workspace.
Refer to the following section to override Global Configuration in each repository with the use of the .whitesource configuration file.
The .whitesource File
A Mend configuration file (.whitesource) can be added to each repository that is enabled for a scan. This file can be added manually to each repository or with the use of Global Configuration. It provides configurable parameter(s) for the Mend scan. The .whitesource file is only added in the default branch of the repository (unless modified, it is the master branch). Any configuration change that is done to this file must be in the default branch of the repository.
We recommend using Global Repo Configuration to set config parameters for all repositories inside a given Organization. However, any .whitesource file can also override parameters set in the global config or even have an isolated configuration (if settingsInheritedFrom global parameter is not set).
NOTE:
By default, all repositories (until specified otherwise in the .whitesource config file) in the integrated Workspace will inherit settings from the whitesource-config repository when it is created and populated with global configuration.
The whitesource-config repository can be located in any project. It is impossible to have more than one repository with the same name in one Workspace. For a better experience, we suggest creating a dedicated project with this repository.
.whitesource file (with settings inherited from the Global Repo Configuration)
{
"settingsInheritedFrom": "whitesource-config/whitesource-config@main"
}.whitesource file (with local configurations)
{
"scanSettings": {
"configMode": "AUTO",
"configExternalURL": "",
"baseBranches": []
},
"buildSettings": {
"createBuildStatus": false
},
"issueSettings": {
"minSeverityLevel": "NONE",
"issueType": "DEPENDENCY"
},
"remediateSettings": {
"workflowRules": {
"enabled": false
}
}
}Parameters
Global Settings
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
settingsInheritedFrom | String | When the global configuration is enabled, this parameter will specify the location of the whitesource-config repository from which it will inherit its configuration. It must contain the Workspace name, repository name, and branch (optional) of the repo-config.json file location. The default branch is 'master', but it can be modified according to the location of the repo-config.json file in the whitesource-config repo. Note: You can override specific parameters that are relevant only in the specific repository by adding these after this parameter. Parameters with the type of array do not override the value from global configuration, but only add new values. Examples: Using only values defined in the global configuration:
JS
JS
| No | N/A |
overrideConfigAllowList | Array | When the global configuration is enabled, this parameter will regulate the ability of repositories that inherit their configuration from the whitesource-config repository to override the parameters locally. There are three options:
Note: This parameter must be used in the repo-config.json file of the whitesource-config repository. | No | null |
Scan Settings (scanSettings)
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
configMode | String | The configuration mode is to be used for each scan. There are three options:
Note: whitesource.config can be provided both in global config and in the repo itself. If it is provided in both places and there are parameters that are set on both levels - repo level will take precedence. | No | AUTO |
configExternalURL | String | The URL of the external configuration file (you can choose any filename). The configuration file content should be in the same format as the Unified Agent configuration file. The following protocols are supported: 'ftp://', 'http://', 'https://'. For example: 'https://mydomain.com/whitesource-settings/wss-unified-agent.config' Notes:
| No | Empty |
baseBranches | Array | Adds the ability to specify one or more base branches for which scanning results will be sent to a new Mend project. Example usage: ["master", “integration"] This will set both master and integration branches as base branches. Notes
| No | Empty In this case, the base branch only consists of the default branch. |
enableLicenseViolations | Boolean | When enabled, a new Mend License Check will be generated for each valid push. Notes:
| No | false |
javaVersion | String | Defines version of Java in the Scanner. Available values: 8, 11, 17. Note: For any projects that are using Gradle versions prior to v7.3, we recommend setting your Java version used by the integration to one of the lower supported versions, 8 or 11, via the | No |
|
repoNameSync | Boolean | When set to | No | false |
skipScanningStage | Object | Controls what stages of scanning process will be skiped for specific package manager. The available parameters are:
All package managers for which a pre-step is available can be specified, e.g., Usage example:
CODE
| No | none |
exploitability | Boolean | When set to Additional information about exploitability is available in the designated Public Exploits page. | No | false |
uaConfigMergeSetting | String | Possible values: Note: All other UA settings are always overridden on a local level. | No | OVERRIDE |
cloneSubmodules | Boolean | If set to Notes:
| No | false |
Build Settings (buildSettings)
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
displayMode | String | How to display Mend security information for a scan performed on a non-base branch:
| No | diff |
createBuildStatus | Boolean | The app can provide checks in commits and pull requests on any repository branch. This parameter defines whether Mend Security Check is going to run. If set to | No | false |
failBuilds | Boolean | The app provides checks in commits and pull requests on any repository branch. This parameter defines the conclusion status for when a Mend Security Check is completed. When the parameter is set to false, the conclusion status of a Mend Security Check will always be 'Success', even if the check fails. This way, any repository member is able to merge a pull request, even if a Mend Security Check found security vulnerabilities. When the parameter is set to true (default), the conclusion status of a Mend Security Check will be 'Failure' in cases where the Mend Security Check found security vulnerabilities or an error occurred during the scan. When this configuration is defined, a policy for approving a pull request is enforced. In this setting, only the administrator of the repository can approve the merging of a pull request that contains one or more checks with a 'Failure' status. | No | true |
failLicenseBuilds | Boolean | The app provides checks in commits and pull requests on any repository branch. This parameter defines the conclusion status for when a Mend License Check is completed. When the parameter is set to false, the conclusion status of a Mend License Check will always be 'Success', even if the check fails. This way, any repository member is able to merge a pull request, even if a Mend License Check found license policy violations. When the parameter is set to true (default), the conclusion status of a Mend License Check will be 'Failure' in cases where the Mend License Check found license policy violations or an error occurred during the scan. When this configuration is defined, a policy for approving a pull request is enforced. In this setting, only the administrator of the repository can approve the merging of a pull request that contains one or more checks with a 'Failure' status. | No | true |
showWsInfo | Boolean | Whether to show additional Mend information such as the project token inside the Mend Build Status (after the scan token). Mend information is only displayed if the commit originated from a base branch. The following hidden JSON object will also be added inside the Build Status when this parameter is enabled:
CODE
Note: Additional Mend data may be added inside the JSON object in the future. | No | false |
strictMode | String | Controls the messaging and status of security and license checks in the case of partial scan results (i.e. Mend Scanner experienced issues pulling some of the project’s dependencies during the scan). The available parameter values are:
Note: For strictMode to work, the vulnerableCheckRunConclusionLevel and licenseCheckRunConclusionLevel parameters must be set to | No |
|
strictModeInfo | Boolean | Controls the inclusion of INFO logs in the Scan Details report.
| No |
|
Issue Settings (issueSettings)
NOTE: Starting with the release of version 22.12.1 (January 2nd, 2022), to take advantage of the Critical label for vulnerabilities for existing Issues created by our repo integration, a new scan must be triggered on the repository. If a scan has not been triggered after upgrading to this version, the repo will continue to only show the previous three labels (High, Medium, Low) for existing Issues. For more information on the Critical setting, please visit our documentation here.
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
minSeverityLevel | String | Enables users to decide whether to open a new Issue only if a certain severity level is available on a detected vulnerability. Available values for minSeverityLevel:
NOTES:
| No | NONE |
minVulnerabilityScore | string | Enables users to define issue creation based on a specified minimum vulnerability CVSS score. Allowed values - floats with one decimal from 0 to 10. For more information on CVSS 3 Scores, click here. Notes:
| No | 0 |
maxVulnerabilityScore | string | Enables users to define issue creation based on a specified maximum vulnerability CVSS score. Allowed values - floats with one decimal from 0 to 10. For more information on CVSS 3 Scores, click here. Notes:
| No | 10 |
displayLicenseViolations | Boolean | Whether to generate an Issue for every detected license policy violation. Note: This parameter is relevant only if enableLicenseViolations (scanSettings) is set to true. | No | true (only if enableLicenseViolations (scanSettings) is set to true) |
issueType | String | Defines which type of the issues will be created in the repository: one for each vulnerability (value: | No |
|
Remediate Settings (remediateSettings)
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
enableRenovate | Boolean | When enabled, Remediate will raise automated Pull Requests for outdated dependencies in addition to Pull Requests remediating vulnerable dependencies. Remediate will then perform all the functionality and support all the configuration options available in Mend Renovate. See Renovate configuration options for all configuration options. | No | false |
workflowRules | Object | This parameter is used to specify the rules that regulate when to open remediation pull requests. Usage examples:
CODE
| Yes |
CODE
|
workflowRules.enabled | Boolean | Enables Workflow Rules being set from a .whitesource file. Note: workflow rules can also be set in the Mend application in the Admin → Integration Workflow Rules. But if this parameter is set to | Yes | false |
workflowRules.minVulnerabilitySeverity | String | The minimal vulnerability severity level to automatically create remediation pull requests for. Allowed values - E.g. if set to Note: If this parameter is used together with minVulnerabilityScore and maxVulnerabilityScore, only minVulnerabilitySeverity will take effect. | No | LOW |
workflowRules.minVulnerabilityScore | Float | The minimal vulnerability CVSS 3 score to automatically create remediation pull requests for. Allowed values - floats with one decimal from 0 to 10. For more information on CVSS 3 Scores, click here. Note: if this parameter is used together with minVulnerabilitySeverity it will not have any effect. | No | Empty |
workflowRules.maxVulnerabilityScore | Float | The maximal vulnerability CVSS 3 score to automatically create remediation pull requests for. Allowed values - floats with one decimal from 0 to 10. For more information on CVSS 3 Scores, click here. Note: if this parameter is used together with minVulnerabilitySeverity it will not have any effect. | No | Empty |
Private Registry Settings (hostRules)
Parameter | Type | Description | Required | Default |
|---|---|---|---|---|
matchHost | String | Defines where the credentials will be applied during the scan. More details are available here.
| No | Empty |
hostType | String | Type of private registry. Supported values: Required if Note: When using Renovate with a Ruby private registry, add a | No | Empty |
userName | String | Used when credentials require username. | No | Empty |
encrypted.password | String | Used when credentials require password, should be encrypted on this page. Encrypted secret that will be applied as a credential to the host set in the
JSON
| No | Empty |
encrypted.token | String | Used when credentials require token, should be encrypted on this page. Encrypted secret that will be applied as a credential to the host set in the
JSON
| No | Empty |
envVariablesMapping | Object | Use this parameter if you used environmental variables in the settings of your package manager to include username and password/token (e.g. for a specified package index).
CODE
or
CODE
Then, set
CODE
| No | Empty |
sourceName | String | This parameter is relevant only for Pipenv private registries. Use this parameter if you don’t have a specified a package index, in this case Mend will create one for you based on other parameters of hostRules. The value of sourceName should be a the index name used for your private packages. For example, if you have packages with such index
CODE
Then set sourceName to
CODE
| No | Empty |
Handling Private Registries and Authenticated Repositories
Private registries hosted on any platform that can be accessed with credentials are supported (Nexus, GitHub, Artifactory, Azure Artifacts, GitLab, NPM).
Supported languages and package managers:
NPM
Yarn
Maven
Gradle
Pip
Pipenv
Go
Nuget
Ruby
SBT
To scan dependencies from private registries and authenticated repositories, Mend must be provided with credentials, such as an NPM token.
To create the encrypted secrets, please follow this link. Each secret you encrypt must be scoped to a Bitbucket Cloud Workspace or repository and its use will be restricted to those within the app. There are the following fields on the encryption page:
Organization\Group - required; your Bitbucket Cloud Workspace to which secrets are to be scoped.
Repository - optional; your Bitbucket Cloud repository to which secrets are to be scoped.
Raw value - required; confidential values/secrets such as tokens or passwords.
Encrypted value - the result of the encryption to be used in the integration.
After the secret is created, these settings should be applied to the hostRules within the repo-config.json (Bitbucket Workspace level) or in the .whitesource file (Bitbucket repository level)
Example of hostRules:
{
"hostRules": [
{
"matchHost": "registry.npmjs.org",
"hostType": "npm",
"userName": "bot1",
"encrypted": {
"token": "3f832f2983yf89hsd98ahadsjfasdfjaslf............"
}
},
{
"matchHost": "https://custom.registry.company.com/maven/",
"hostType": "maven",
"userName": "bot1",
"encrypted": {
"password": "p278djfdsi9832jnfdshufwji2r389fdskj........."
}
}
]
}Asymmetric public-key cryptography of the PGP methodology is used. There is a public key on the page provided for encrypting secrets from passwords or tokens. This public key has a related private key secured by Mend. The private key is used to decrypt secrets created with the public key. In this way, only the holder of the private key (Mend in this situation) can have access to the encrypted contents. Organization/Group, Repository, Raw Value - all information you provide on the encryption page is secured with this approach.
NOTE:
The private registry settings hostRules should be added to the repo-config.json.
The 'organization/group' field on the encrypt config should match the Bitbucket workspace name to which you have onboarded Mend.
Notes for NPM private registries:
To connect to private registries the .npmrc file of the scanned project is used. It is either edited (
hostRulesfrom the config are applied) or created for scanning purposes.If .npmrc is missing and only one host is used in the project it should be connected to the official http://npmjs.com . Otherwise, only private dependencies will be scanned and all public dependencies of this registry will be omitted.
If several hosts are used in the project it is required that .npmrc file exists in the project and contains information about these hosts.
Notes for Yarn private registries:
For Yarn 1 projects, to connect to private registries the .npmrc file of the scanned project is used. For Yarn 2/3 .yarnrc is used. It is either edited (
hostRulesfrom the config are applied) or created for scanning purposes.If .yarnrc is missing (or
npmRegistryServerin it is not set) and only one host is used in the project, it will be set to thehostRules.matchHostfrom the config. In the same case, if several hosts are used,npmRegistryServerwill be set to https://registry.yarnpkg.com.
Notes for Maven private registries:
To connect to private registries the settings.xml file of the scanned project is used. It is either edited (
hostRulesfrom the config are applied) or created for scanning purposes.
Notes for Gradle private registries:
To connect to private registries the build.gradle or settings.gradle file of the scanned project is used. For both these files, the kotlin (.kts) format is supported.
The buildscript or pluginManagement blocks must be at the beginning of the
build.gradleorsettings.gradlerespectively.matchHostshould contain the full path to the private registries, not just the domain.
Notes for Nuget private registries:
To connect to private registries, the NuGet.Config file of the scanned project is used. It is either edited (
hostRulesfrom the config are applied) or created for scanning purposes.
Notes for Pip private registries:
Certain special characters are not valid in the credential part of a URL. If the user or password part of the login credentials contains any of these special characters, they must be percent-encoded.
Notes for Pipenv private registries:
Use either envVariablesMapping or sourceName when setting host rules.
Notes for Go private registries:
To connect to private registries, the .netrc file of the scanned project is used. It is either edited (
hostRulesfrom the config are applied) or created for scanning purposes.Only HTTPS is available for
matchHost; HTTP is not supported.If the private registry is hosted on GitHub, only
tokencan be used in theencrypted(i.e.,passwordis not supported).
Automate Secret Encryption for Private Registries
You can encrypt secrets from the CLI, using the curl, echo, jq, gpg, grep and tr CLI programs.
Here is an example:
curl https://app.renovatebot.com/renovate.pgp --output renovate.pgp
echo -n '{"o":"your-organization", "r":"your-repository (optional)", "v":"your-secret-value"}' | jq . -c | gpg --encrypt -a --recipient-file renovate.pgp | grep -v '^----' | tr -d '\n'
The above script uses:
curlto download the Mend Renovate hosted app's public keyechoto echo a JSON object intojqjqto validate the JSON and then compact itgpgto encrypt the contentsgrepandtrto extract the encrypted payload which we will use
The jq step is optional, you can leave it out if you wish. Its primary value is validating that the string you echo to gpg is valid JSON and compact.
Note: Encrypted secrets must have at least an org/group scope, and optionally a repository scope. This means that Renovate will check if a secret's scope matches the current repository before applying it, and warn/discard if there is a mismatch.
Encrypted secrets usually have a single organization. But you may encrypt a secret with more than one organization, for example, org1,org2. This way the secret can be used in both the org1 and org2 organizations.
For more information on how to use secrets for private packages, refer to the Private package support documentation.
Supported Dependency Files
The following dependency files are supported for Mend for Bitbucket Cloud SCA scans:
bower.json
build.gradle
build.gradle.kts
build.sbt
conanfile.py
conanfile.txt
cargo.toml
composer.json
dependencies.scala
environment.yml
Gemfile.lock
glide.lock
go.mod
Godeps.lock
gogradle.lock
Gopkg.lock
gradle.lockfile
gradle.properties
libs.gradle
libs.versions.toml
package-lock.json
package.json
paket.dependencies
packages.config
packages.lock.json
packrat.lock
Pipfile
pipfile.lock
pnpm-lock.yaml
Podfile
poetry.lock
pom.xml
pubspec.yaml
pyproject.toml
requirements.txt
settings.gradle
setup.cfg
setup.py
vendor.conf
versions.kt
yarn.lock
Any metafile with one of the following extensions:
asp
aspx
config
csproj
do
gitmodules
htm
html
jsp
shtml
tf
xhtml
Cargo.lock
