Overview
The Search Findings tool allows you to quickly locate and observe findings in your Applications and Projects within your Organization. The search method you choose depends on whether you focus on a particular library or finding.
Notes:
-
The Search Findings will show results of CVEs or library names of different Applications or Projects available in your organization on the Mend AppSec Platform. It will not provide detailed descriptions of all known CVEs or their impacts.
-
The Search Findings tool is available for Dependencies (SCA) and Containers.
Search Dependency Findings
-
Click Findings on the top-bar menu of the Mend AppSec Platform UI.

-
From the left menu pane, select Dependencies.
-
Search for vulnerabilities using the available filters.
-
Default filters:
-
Library: Enter at least three characters of the library name or full name to search for matching libraries in your inventory.
-
Finding Id: Must be complete and case sensitive (e.g., CVE-2023-1234).
-
Zero-Day Event: Select an available event from the drop-down list.
Combine all three to narrow the list down. Example: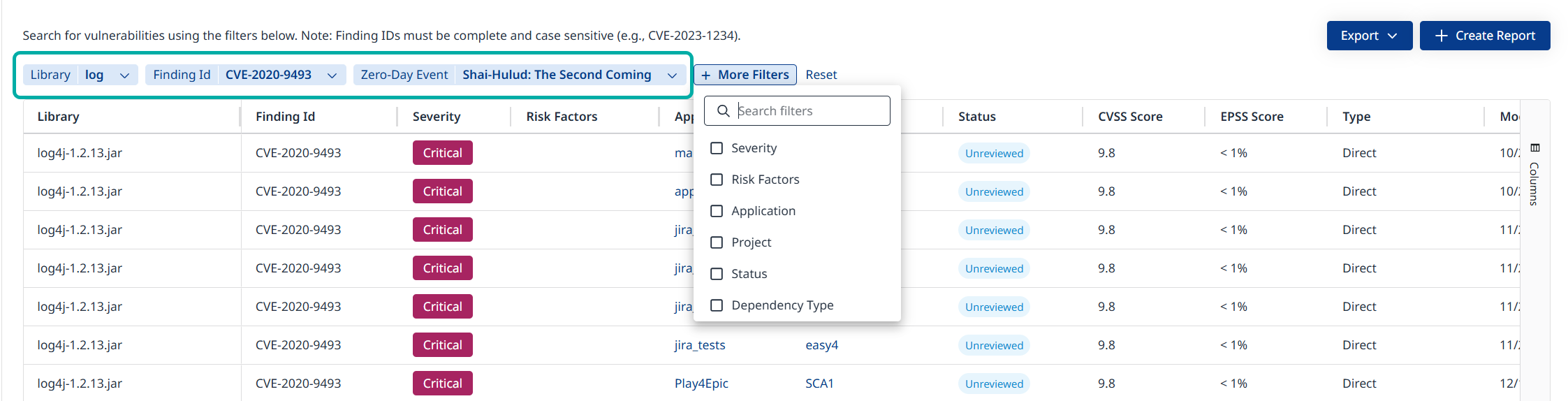
You can add more filters to narrow the list down even further.
-
-
Additional filters:
-
Severity
-
Risk Factors
-
Application
-
Project
-
Status
-
Dependency Type
-
-
-
Click anywhere on the row to open the finding side-panel.
Search Result Columns
The following table provides descriptions for each column displayed in your search results.
|
Search Result Fields |
Description |
|---|---|
|
|
The name of the library affected by the finding |
|
|
The identifier of the finding in the affected Library |
|
|
The severity level ( |
|
|
Lists risk factors applicable for the finding in question (e.g., “Reachable”) |
|
|
The application containing the affected project |
|
|
The name of the project this finding affects |
|
|
Indicates the status of a finding, which can be one of the following: Unreviewed, In Review, Issue Created, Remediated, or Suppressed For more information on Mend SCA statuses, please check out our Mend SCA statuses documentation. |
|
|
The CVSS score is a numerical value ranging from 0.0 to 10.0 that represents the severity of a finding |
|
|
The EPSS score represents the likelihood of exploiting a vulnerability |
|
|
Denotes whether the dependency is Direct or Transitive |
|
|
The date of the last modification |
|
|
The date when this finding was first detected |
|
|
Date when the finding was published |
|
|
CVSS Type: The CVSS type refers to the version of the CVSS standard being used |
|
|
Displays the reason provided by the user for suppressing the finding (where applicable) |
|
|
In case you have a source file it will show up here |
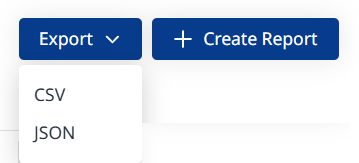
Export your Findings or Create a Report
As a security or compliance user, you may want the ability to export the vulnerability/library search results from the “Findings” page, for further analysis, sharing with stakeholders, or storing for auditing purposes.
Two options are available to you at the top-right corner of the screen:
-
Export: Click to download the data currently displayed on screen in CSV or JSON format.
-
+ Create Report: Click to launch the Dependencies Findings report wizard.
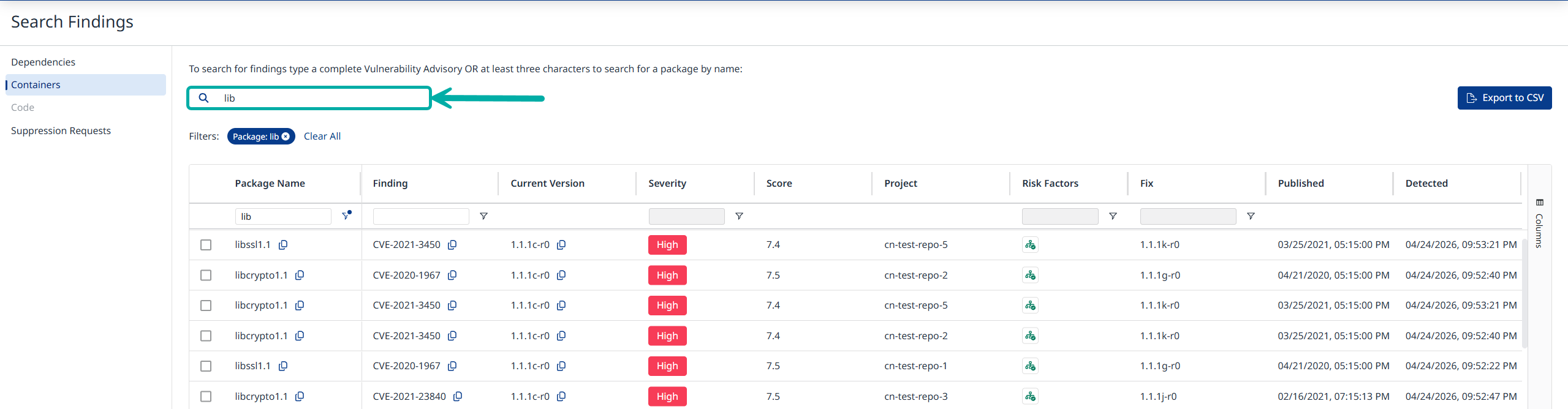
Search Container Findings
-
Click Findings on the top-bar menu of the Mend AppSec Platform UI.

-
From the left menu pane, select Containers.
-
Type a complete Vulnerability Advisory ID OR at least three package name characters.
-
Click Export to CSV at the top-right to download the currently displayed data in CSV format.
Search Result Columns
The following table provides descriptions for each column displayed in your search results.
|
Search Result Fields |
Description |
|---|---|
|
|
The name of the package affected by the finding |
|
|
The identifier of the finding in the affected package |
|
|
The current version of the package in your inventory |
|
|
The severity level ( |
|
|
The severity score (0-10.0) |
|
|
The name of the project this finding affects |
|
|
The application containing the affected project |
|
|
Lists risk factors applicable for the finding in question (e.g., “Reachable”) |
|
|
The package version which contains the fix |
|
|
Date when the finding was published |
|
|
The date when this finding was first detected |