SAML Configuration
Note: The legacy Mend SAST application was deprecated on April 1st, 2025. For assistance with migrating to the Mend AppSec Platform, please contact your customer success manager or the success team at success@mend.io.
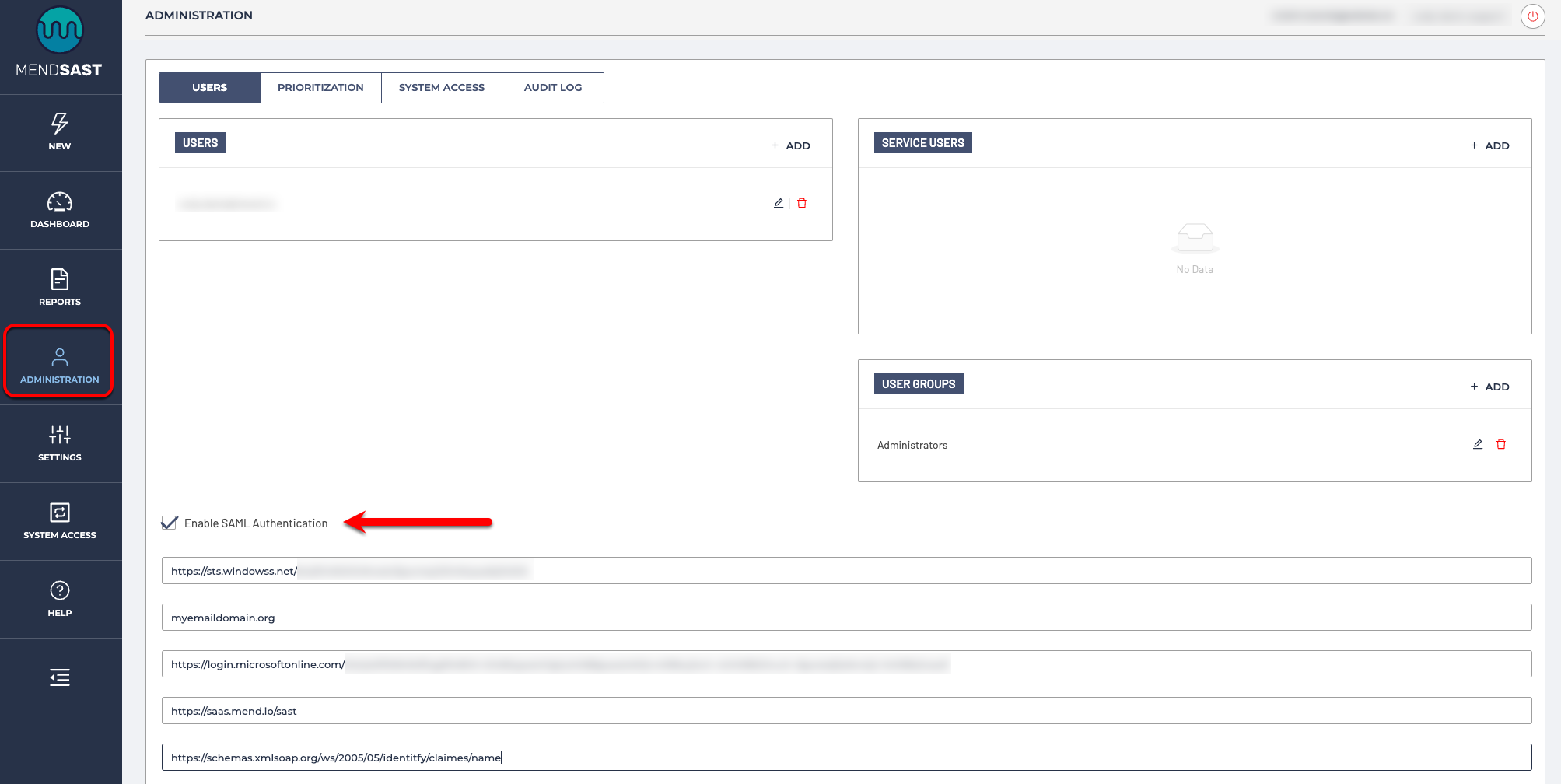
Mend SAST® supports SAML as an alternative authentication method. To configure SAML, navigate to Administration -> Users and check Enable SAML Authentication:
Mend SAST® service provider configuration
In SAML terms, Mend SAST® is a Service Provider (SP), i.e., the entity providing the service. As such, it requires the following configuration:
Entity ID: your organization's unique SAML ID which can be found in your IdP’s SAML metadata, usually as an entityID tag)
Domain: your organization’s email domain. If your organization uses multiple email domains, you can provide them here in a comma-separated list.
IdP Metadata URL: a link to your IdP's metadata file
Note: A metadata URL is the only option supported by the Mend SAST SAML configuration. For IdP’s like Google that do not support a direct metadata URL, you will instead need to externally host your metadata XML file and provide this URL in the Mend SAST IdP Metadata URL setting.
Root URL: root URL of your Mend SAST application, for example, https://saas.mend.io/sast/
Note: The root URL must end with “/sast”.
Username Attribute: the SAML username contained in the metadata file
Mapping SSO users to Mend SAST® roles can be done in the Role Mapping section using attributes. If no role mapping is configured or matched, the configured Default Role will be assigned to logged-in users.
Mapping of SSO users to Mend SAST® groups can be done in the Group Mapping section using attributes. If no group mapping is configured or matched, the default "SSO Users" group will be assigned to logged-in users.
Mend SAST will sign all requests by default. This will not affect some of the popular identity providers like Okta and Azure that do not validate AuthnRequest signatures as the parameters are ignored.
Mend SAST® SAML and IdP examples
Below are examples of popular IdPs and how to configure them with our SAST SAML offering:
